US nuclear launch code hacked?
Shares
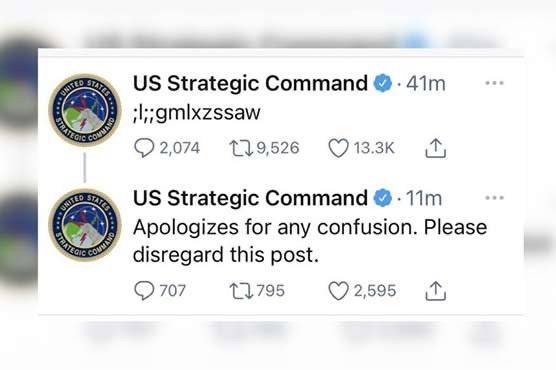
WASHINGTON - Some jokingly said the cryptic tweet, ";l;;gmlxzssaw," was a US nuclear launch code. Others, that the Pentagon had been hacked.
And some even thought it was a signal to political conspiracists.
Now the US Strategic Command, which runs the country’s powerful nuclear weapons force, says the enigmatic posting on its Twitter account in fact came from the hands of a precocious kid.
Headquartered in Offutt Air Force Base, Nebraska, Stratcom manages the US military’s strategic deterrence -- that is, the massive nuclear weapons force and missile defenses that are designed to discourage any attack against the country by other powers.
So its media comments are closely watched for signs of any change in its current defense stance.
But Stratcom told reporter Mikael Thalen of the Daily Dot that the tweet was no secret message, and was instead was the result of a Stratcom social media editor working from home.
"The Command’s Twitter manager, while in a telework status, momentarily left the Command’s Twitter account open and unattended. His very young child took advantage of the situation and started playing with the keys and, unfortunately, and unknowingly, posted the tweet," Stratcom official Kendall Cooper said in a letter Thalen posted on line.
"Absolutely nothing nefarious occurred, i.e. no hacking of our Twitter account."
Thirty minutes later Stratcom tweeted to disregard the previous tweet, and then both of those messages were deleted.
It is not the first time Stratcom has run into trouble on social media.
In December 2018, referring to the Times Square New Year’s Eve ball-drop in New York, it joked on Twitter about it being prepared to drop something "much bigger," with a video of a B-2 stealth bomber dropping two bombs to the beat of pulsing music.
Hours later it deleted that tweet and apologized that it was "in poor taste." -APP/AFP
